Windows-Exploit-Suggester(Windows下提权辅助工具)
此道具是这款很好用的Windows下提权辅助软件(早已适用Windows 10下的提权了),中国早已有很多人到用了,可是始终沒有相对的汉语word表格,因此我简一瓷砖翻泽了一会儿,水准有现,如无不正确,热情接待强调,感谢。
叙述
该道具能够将目的体系的傻瓜包安裝状况与苹果公司的木马病毒数据表开展比照,从而检验出目的体系中不确定性的未修复漏洞。一起此道具还会告之客户对于今以木马病毒是不是有公布的exp和能用的Metasploit模快。
一起它能够应用–update叁数去智能化地从微软下载漏洞补丁数据表,并将其以Excel报表的方式储存。
必须留意的是,此道具最先会假设目的体系存有全部木马病毒,随后再应用场景漏洞补丁状况去相关性的清除已修复木马病毒。此志道具将会会导致某些误报,因而你最先必须知道目的设备装上什么手机app。比如,假如此设备沒有IIS的傻瓜包,即便设备上沒有IIS,道具也一样会觉得存有此木马病毒。
此道具挺大水平中受了Pentura的linux_Exploit_Suggester的启迪。
使用方法
1.首先需要更新漏洞数据库
$ ./windows-exploit-suggester.py --update
[*] initiating...
[*] successfully requested base url
[*] scraped ms download url
[+] writing to file 2014-06-06-mssb.xlsx
[*] done
2.然后安装程序依赖:python-xlrd
watcher@ubuntu:~/xlrd-0.9.4/xlrd-0.9.4$ sudo python setup.py install
[sudo] password for watcher:
running install
running build
running build_py
running build_scripts
running install_lib
creating /usr/local/lib/python2.7/dist-packages/xlrd
copying build/lib.linux-x86_64-2.7/xlrd/compdoc.py -> /usr/local/lib/python2.7/dist-packages/xlrd
......
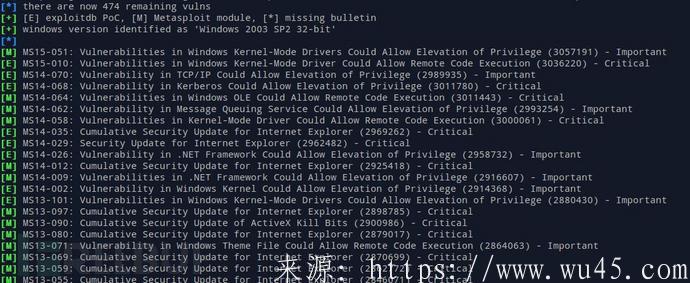
3.接着在目标机器中执行systeminfo,并将其输出到文件中,然而带入参数–systeminfo中,并指定数据库位置(就是那个excel文件)
$ ./windows-exploit-suggester.py --database 2014-06-06-mssb.xlsx --systeminfo win7sp1-systeminfo.txt
[*] initiating...
[*] database file detected as xls or xlsx based on extension
[*] reading from the systeminfo input file
[*] querying database file for potential vulnerabilities
[*] comparing the 15 hotfix(es) against the 173 potential bulletins(s)
[*] there are now 168 remaining vulns
[+] windows version identified as 'Windows 7 SP1 32-bit' [*]
[M] MS14-012: Cumulative Security Update for Internet Explorer (2925418) - Critical
[E] MS13-101: Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (2880430) - Important
[M] MS13-090: Cumulative Security Update of ActiveX Kill Bits (2900986) - Critical
[M] MS13-080: Cumulative Security Update for Internet Explorer (2879017) - Critical
[M] MS13-069: Cumulative Security Update for Internet Explorer (2870699) - Critical
[M] MS13-059: Cumulative Security Update for Internet Explorer (2862772) - Critical
[M] MS13-055: Cumulative Security Update for Internet Explorer (2846071) - Critical
[M] MS13-053: Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Remote Code Execution (2850851) - Critical
[M] MS13-009: Cumulative Security Update for Internet Explorer (2792100) - Critical
[M] MS13-005: Vulnerability in Windows Kernel-Mode Driver Could Allow Elevation of Privilege (2778930) - Important
[*] done
下面这条指令可以列出指定操作系统版本存在的所有可能EXP(假设目标系统没有打任何补丁)
$ ./windows-exploit-suggester.py --database 2014-06-06-mssb.xlsx --ostext 'windows server 2008 r2' [*] initiating...
[*] database file detected as xls or xlsx based on extension
[*] getting OS information from command line text
[*] querying database file for potential vulnerabilities
[*] comparing the 0 hotfix(es) against the 196 potential bulletins(s)
[*] there are now 196 remaining vulns
[+] windows version identified as 'Windows 2008 R2 64-bit' [*]
[M] MS13-009: Cumulative Security Update for Internet Explorer (2792100) - Critical
[M] MS13-005: Vulnerability in Windows Kernel-Mode Driver Could Allow Elevation of Privilege (2778930) - Important
[E] MS11-011: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (2393802) - Important
[M] MS10-073: Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (981957) - Important
[M] MS10-061: Vulnerability in Print Spooler Service Could Allow Remote Code Execution (2347290) - Critical
[E] MS10-059: Vulnerabilities in the Tracing Feature for Services Could Allow Elevation of Privilege (982799) - Important
[E] MS10-047: Vulnerabilities in Windows Kernel Could Allow Elevation of Privilege (981852) - Important
[M] MS10-002: Cumulative Security Update for Internet Explorer (978207) - Critical
[M] MS09-072: Cumulative Security Update for Internet Explorer (976325) - Critical
许可
本程序为自由软件;您可依据自由软件基金会所发表的GNU 通用公共授权条款,对本程序再次发布和/ 或修改;无论您依据的是本授权的第三版,或(您可选的)任一日后发行的版本。
本程序是基于使用目的而加以发布,然而不负任何担保责任;亦无对适售性或特定目的适用性所为的默示性担保。详情请参照GNU 通用公共授权。
相关文章
- 2条评论
 寻妄折木2022-05-29 00:00:50
寻妄折木2022-05-29 00:00:50- g vulns[+] windows version identified as 'Windows 2008 R2 64-bit' [*] [M] MS13-009: Cumulative Security
 礼忱苍阶2022-05-28 14:58:41
礼忱苍阶2022-05-28 14:58:41- ws 2008 R2 64-bit' [*] [M] MS13-009: Cumulative Security Update for Internet Explorer (

 滇ICP备19002590号-1
滇ICP备19002590号-1